Tuesday, February 21, 2017
Kali Linux Tutorial Hack A Web Browser Using BeEF
Kali Linux Tutorial Hack A Web Browser Using BeEF

Step 1: Start Cooking BeEF
BeEF is built into Kali Linux, and it can be started as a service and accessed via a web browser on your localhost.
Here is a complete tutorial about hackers OS Kali Linux, so read this before you go ahead: An Introduction To Hacker’s OS: Kali Linux Setup Tutorial
So let’s start by firing up Kali and cooking a bit of BeEF. Start the BeEF service by going to “Applications” -> “Kali Linux” -> “System Services” -> “BeEF” -> “beef start.”

Step 2: Opening a Browser to BeEF
The BeEF server can be accessed via any browser on our localhost (127.0.0.1) web server at port 3000. To access its authentication page, go to:
http://localhost:3000/ui/authentication
The default credentials are “beef” for both username and password.

Great! Now you have successfully logged into BeEF and are ready to begin using this powerful platform to hack web browsers.
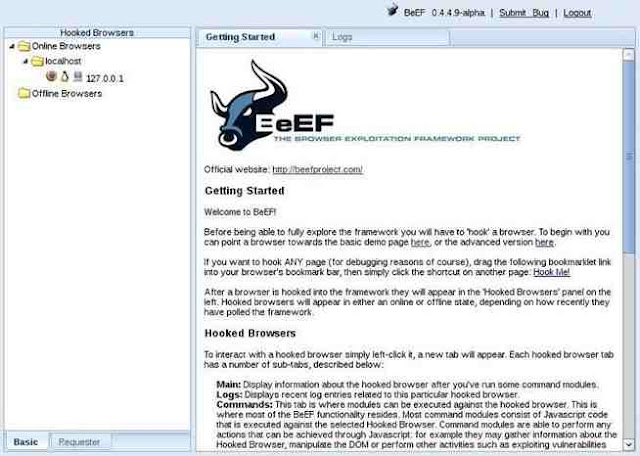
Note that in the screenshot below that my local browser, 127.0.0.1, appears in the left hand “Hooked Browsers” explorer after I clicked on the link to the demo page. BeEF also displays its “Getting Started” window to the right.
Note that in the screenshot below that my local browser, 127.0.0.1, appears in the left hand “Hooked Browsers” explorer after I clicked on the link to the demo page. BeEF also displays its “Getting Started” window to the right.
Step 3: Viewing Browser Details
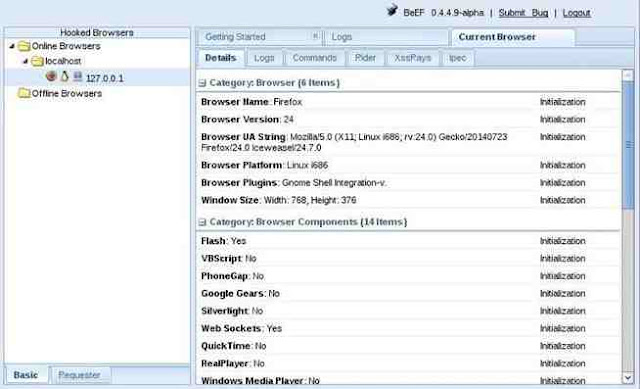
If I click on the local browser, it will provide with more choices to the right including a “Details” window where we can get all the particulars of that browser. Since I am using the Iceweasel browser built into Kali, which is built upon Firefox, it shows me that the browser is Firefox.
It also shows me the version number (24), the platform (Linux i686), any components (Flash, web sockets, etc.), and more information that we will be able to use in later web application hacks.
Step 4: Hooking a Browser
The key to success with BeEF is to “hook” a browser. This basically means that we need the victim to visit a vulnerable web app. This injected code in the “hooked” browser then responds to commands from the BeEF server. From there, we can do a number of malicious things on the victim’s computer.
BeEF has a JavaScript file called “hook.js,” and if we can get the victim to execute it in a vulnerable web app, we will hook their browser! In future tutorials, we will look at multiple ways to get the victim’s browser hooked.
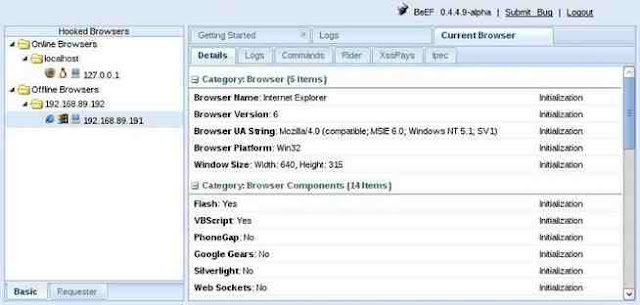
In the screenshot below, I have “hooked” an Internet Explorer 6 browser on an old Windows XP on my LAN at IP 192.168.89.191.
Step 5: Running Commands in the Browser
Now, that we have hooked the victim’s browser, we can use numerous built-in commands that can executed from the victim’s browser. Below are just a few examples; there are many others.
- Get Visited Domains
- Get Visited URLs
- Webcam
- Get All Cookies
- Grab Google Contacts
- Screenshot
In the screenshot below, I selected the “Webcam” command that many of you may be interested in. As you can see, when I execute this command, an Adobe Flash dialog box will pop up on the screen of the user asking, “Allow Webcam?” If they click “Allow,” it will begin to return pictures from the victim’s machine to you.
Of course, the text can be customized, so be imaginative. For instance, you could customize the button to say “You have just won the lottery! Click here to collect your winnings!” or “Your software is out of date. Click here to update and keep your computer secure.” Other such messages might entice the victim to click on the box.

Step 6: Getting Cookies
Once we have the browser hooked, there is almost unlimited possibilities of what we can do. If we wanted the cookies of the victim, we can go to “Chrome Extensions” and select “Get All Cookies” as shown in the screenshot below.

When we click on the “Execute” button to the bottom right, it will begin collecting all the cookies from the browser. Obviously, once you have the user’s cookies, you are likely to have access to their websites as well.
BeEF is an extraordinary and powerful tool for exploiting web browsers. In addition to what I have shown you here, it can also be used to leverage operating system attacks. We will be using it and other tools in my new series on hacking web applications, mobile devices, and Facebook, so keep coming back, my greenhorn hackers.
Recommended Articles To Become A Hacker:
How To Become A Hacker - Basic Guide For Beginners 2015
Understand The Hacker Mindset To Become A Real Hacker
Programming Languages For Hackers And Learn It From Most 6 Helpful Websites
Installing Hackers OS Kali Linux In VMware (Beginners Guide With Screenshots)
Easy Steps to Create Web Penetration Testing Lab in Kali Linux
Introduction to using Metasploit in Kali Linux
An Introduction To Hacker’s OS: Kali Linux And Setup Tutorial.
Linux Powerful Distros For Hacking Or Security: Kali, Tails And Qubes
Become A Hacker: What Is Denial of Service (DoS) Attack?
Available link for download